
Computer forensics is a crucial security area that involves a structured and rigorous investigation to uncover vital evidence from victimized devices. The primary objective of computer forensic investigation is to trace the sequence of destructive events or activities and finally reach the offender. A significant rise in cyberattacks has drastically increased the demand for skilled forensic investigators. The step-by-step process to conduct forensic investigation involves:

1. Preliminary Analysis:
It is essential for forensic investigators to initiate a preliminary analysis to figure out the critical details of a cybercrime. The analysis must include a thorough assessment of the case to devise the best approach to investigating its intricacies. The forensic analyst takes notes about the system under surveillance taking into consideration factors such as the role of the system in the organizational structure and network, configured operating system, custom specifications, RAM, and the system location. An In-depth preliminary analysis helps in devising effective strategies for investigating the crime.
2. Evidence Acquisition:
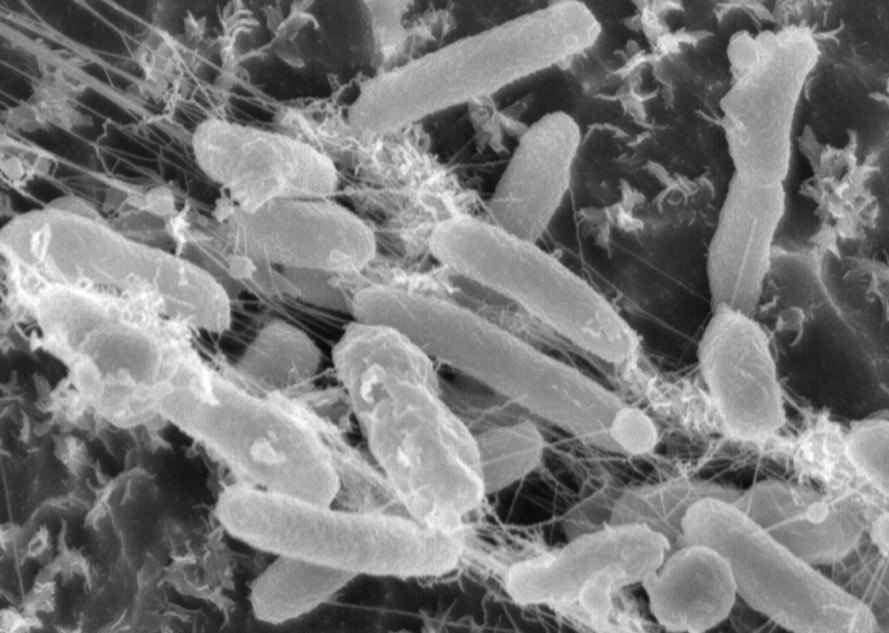
Evidence acquisition refers to collecting the maximum amount of data (both volatile and non-volatile) from all the likely sources and verifying the data integrity. Collection of volatile data is subject to changes and requires special attention of the involved analysts. Volatile data includes login session details, network connections, RAM content caches, and running processes. Nonvolatile data verification calls for the hard disk investigation. Involving business owners at this stage proves helpful in determining the business impact of the planned investigation strategy.
3. Evidence Identification:
This step calls for assessing and identifying the potential evidence and presenting it in a digital format so that it can be easily understood. All the acquired raw data needs to be organized by using the Forensic Tool Kit (FTK), Mobile Phone Examiner, and dtSearch tools.
4. Evaluation:
This key step lets you decide if the gathered potential forensic investigation evidence can be used to draw legal conclusions. Every collected evidence is assessed on various grounds to analyze if it can be presented legally during a trial and if it can direct the case towards expected conclusions. To perform a successful evaluation, you must preserve the collected data and create an event timeline, perform media and artifact analysis, string search, and employ data recovery tools to authenticate the collected evidence to complete the investigation
5. Reporting and Documentation:
Reporting and documenting the analyzed results involve communicating the details of the performed actions, recommendations to improve the procedures, and the guidelines and tools used during the investigation. Final reports are shared with the parties associated with the governing body of law.
Three Popular Types Of Computer Forensics Certification
One of the most exciting fields to emerge in recent years is that of computer forensics. In order to become a computer forensics specialists you will need to get both proper computer forensics training and certification. In terms of certification, there are three popular certificates available to those considering becoming a computer forensics specialist.
By far the most well known is the CCFE, or the Certified Computer Forensics Examiner. To receive this certificate, you must be able to have knowledge in several different different areas, such as different investigation procedures, the tools that are used in computer forensics, recovery processes for hard disks and digital device and law ethics and legal questions and issues.
The CCFE certificate requires you take a three hour written exam as well as pass a hands on computer forensics testing process. To successfully pass, you will need to receive at least an 80% on the exams.
There are two other common certificates available as well that those who are interested in becoming a computer forensics specialist might want to consider. One as a Certified Information Systems Security Specialist (CISSP) and the other as a Certified Computer Examiner (CCE). The CISSP is an international standards examination for the computer forensics industry, and requires that you already have four years of experience in the computer forensics field. The CCE only requires 18 months of professional experience, and you will have to pass both an online examination and an examination of some test media.
For the best choices in this field, you will want both college level training in a computer related field (such as computer science) as well as pass at least one of these certificate examinations. Computer forensics is a field that will undoubtedly experience major growth in the future, as technology systems become both more sophisticated and hackers and other cyber criminals become more adept and prolific. For those looking for an exciting job in the computer field, computer forensics can be a rewarding choice!
Becoming A Computer Forensics Expert: What Kind Of Coursework Is Needed?
Computer crime is on the rise, and a specific kind of specialist is now in high demand: the computer forensics specialist. Jobs in the computer forensics industry are experience huge growth and are well paid. But if you are considering this field of study, you will likely be wondering about what exactly is needed in terms of computer forensics training in order for you to succeed.
Training in computer forensics is focused on preparing you to accurately gather and analyze computer data. Often your work will form the basis of a court case, so you also need to learn how to properly fill out the paperwork needed for these cases as well. You may also be given tasks involving the safeguarding of computer systems, particularly for jobs in the private industry.
As a computer forensics expert, you will need to know how to recover lost, stolen or destroyed data on a wide variety of computing systems. Not only do you need to be proficient with personal computers and laptops, but you may also need to retrieve data from blackberries, cell phones and even digital cameras.
For those with an interest in intelligence and crime, a degree in computer forensics can be quite exciting and interesting. Although you can be certified in the field in as little as two years of training online, you may also want to consider pursuing a full four years of study (or even a master’s degree) for the most lucrative and well paid positions in the field.
You may want to check out the many online computer forensics training programs available as well as your local colleges to learn more about the courses and classes you will be taking. However, you can be certain that any program will offer a general overview of what the field of computer forensics involved as well as more specialized training in how to use sophisticated computer forensics software programs such as Paraben and EnCase, as well as the basics about how files are hidden on computers and other digital devices, and how to recover them; how to fill out the chain of custody paperwork necessary for court cases, plus many other specialized classes on computer forensics techniques.
For those who have an interest in computers and crime, however, training in the computer forensics field can be both fun and rewarding!
Why Computer Forensics Training Is Important
The skills of a computer forensics are increasingly needed as we move into the digital age and for this reason, computer forensics training is also increasingly important as well. Computer forensics jobs use the latest science and technology to analyze, collect and provide the proof needed in civil and criminal courts to convict those suspected of crimes involving computer hardware and technology. In fact, the very word “forensics” means “to bring to the courts” and it a very important profession in today’s world where crimes involving the theft of identity, technology and on the rise.
However, computer forensics specialists do not merely work on bringing cyber-criminals to justice. They can also be invaluable to corporations to help repair damaged and corrupt data, to prevent unwanted attacks and intrusions of their computer networks, and retrieve lost data.
In fact, the IT budget for computer and network security is one of the largest growing portions of many companies expenditures. The International Data Corporation reported in 2006 that nearly $1.5 billion dollars was spent in 2006 on software to help corporations prepare against cyber attacks, and that number is certainly expected to rise in the very near future. The number of hackers are on the rise, and some specialists have proclaimed we are in the midst of an all out cyber-war when it comes to protecting national and security secrets. Corporations and organizations are pouring large amounts of money into developing state of the art security systems, such as intrusion detection systems, advance firewall configurations and more.
Still, even these steps are often not enough, and when an attack occurs and data is compromised, a computer forensics specialist is needed to help gather and analyze the evidence in order to prevent future attacks. A computer forensics investigator must be properly trained in how to collect data and use the appropriate software and tools needed to repair encrypted or damaged files or recover data that had been deleted.
Generally, a computer forensics specialist will focus on two forms of data: Persistent and Volatile Data. Persistent data is that data which is stored on drives and disks regardless whether the device is powered on or off. Volatile data, on the other hand, will be lost when the computer loses power. This data is usually stored in the RAM and caches, and it can be very difficult to recover without the skills of a trained computer forensics expert.
Computer forensics is certainly one of the most exciting and growing fields is today’s corporate environment. It is for this reason that computer forensics training is in high demand and that this is expected to be a growing industry for years to come.
Conclusion
The Computer Hacking Forensics Investigator (CHFI) certification covers the wide array of diverse computer investigation tools, techniques, and processes that help you in identifying the legal evidence of cyberattacks.
NetCom Learning offers a CHFI training and certification course illustrating the latest forensic investigation tools, techniques, and fundamentals for effective database, mobile, cloud, and network forensic investigations. We enable you to acquire hands-on experience with key forensic investigation techniques and the standard forensic tools essential to legally pursue cyberattack perpetrators.






Awesome just absolutely awesome blog. Thanks for sharing.1
Thank you.
I love reading a post that will make men and women think.
Also, many thanks for allowing for me to comment!
Great stuff to read about computer forensics here. Thank you
Thank you. Appreciate it.
It’s awesome designed for me to have a website, which is useful for my experience.
thanks admin
Thank you. Appreciate it.
Great Blog – Thank you for sharing about computer forensics.
Greetings from Idaho! I’m bored to death at work so I decided to browse your website on my iphone during lunch break.
I really like the info you present here and
can’t wait to take a look when I get home. I’m amazed at how quick your blog loaded on my phone ..
I’m not even using WIFI, just 3G .. Anyhow, great blog!
Pretty! This has been a really wonderful post. Many thanks for providing these details.
Thank you.
What I find most interesting in computer forensic investigations is when you collect the most number of evidence from all sources to validate the integrity of data. My nephew Mark would surely go crazy about learning how to pick up clues of corruption or theft from volatile data like log sessions, network connections, and running processes. He’s into gadgets and tech, and he’d sure want to consider being a computer forensics expert someday.
Right here is the perfect website to know about computer forensics in details.
Thank you for the auspicious writeup.
Very true and well said. Thank you